TL;DR:
- Bitcoin is analyzing a proposal called BIP-361 that seeks to freeze 6.9 million coins in old wallets to resist quantum attacks.
- The three-phase plan includes disabling legacy signatures and could render unmigrated funds permanently unusable after a deadline.
- The community rejects the proposal, arguing that freezing other users’ funds violates the fundamental principle of sovereignty over one’s own assets.
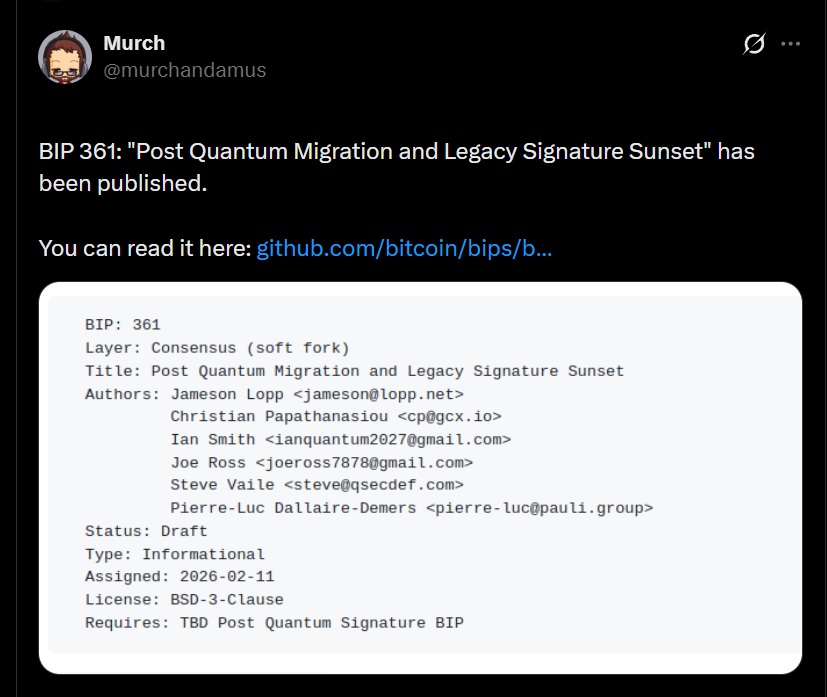
The world of Bitcoin development is in the midst of one of its most delicate debates in years. In April 2026, a group of developers led by cypherpunk Jameson Lopp presented proposal BIP-361, an upgrade scheme designed to protect the network against the threat posed by quantum computers. The underlying problem: approximately 34% of Bitcoin’s total supply, around 6.9 million coins, remains in legacy addresses vulnerable to this type of attack, including wallets attributed to Satoshi Nakamoto.
The proposal builds on previously introduced work, BIP-360, which introduced a more secure address type called Pay-to-Merkle-Root (P2MR), comparable to Taproot but with greater cryptographic resistance. Developers present it as a soft fork that does not alter the network’s current functionality.
The Three-Phase Plan Divides the Bitcoin Community
The scheme envisions a gradual transition. In a first stage, sending new funds to legacy addresses would be prohibited. Five years after activation, those signatures could be fully disabled, leaving unmigrated funds permanently inaccessible. A third phase contemplates a recovery mechanism based on zero-knowledge proofs for users who still hold their keys.
Supporters of the plan argue that freezing inactive coins works as an upgrade incentive. They also contend that if a quantum computer managed to break legacy addresses and steal funds on a massive scale, the damage to confidence in Bitcoin would be irreparable.
Outside the BIP-361 debate, developer Olaoluwa Osuntokun presented an independent prototype that allows users to recover funds using zk-STARK proofs without exposing private keys. The system runs in approximately 50 seconds on a conventional computer, uses 12 GB of RAM and generates a 1.7 MB proof file.
Financial Sovereignty Against Protocol Protection
The Bitcoin community’s response was immediate and largely critical. The central argument is that no developer or group should have the ability to lock another user’s funds. The “not your keys, not your coins” principle implies, according to critics, that whoever controls their keys retains their coins without conditions or deadlines.
Phil Geiger, from Metaplanet, summed up the contradiction precisely: “We have to steal people’s money to prevent it from being stolen.” The underlying concern is that establishing a precedent for freezing opens the door to future interventions under different justifications. BIP-361 remains a proposal with no active implementation.