TL;DR:
- KelpDAO held LayerZero responsible for the April 18 exploit that caused losses of over $300 million.
- Independent researchers from SEAL 911 confirmed the breach occurred within LayerZero’s infrastructure perimeter, not due to a Kelp configuration error.
- The protocol will migrate rsETH to Chainlink CCIP, whose oracle network handled over $30 trillion in value across more than seven years of operation.
KelpDAO publicly challenged LayerZero‘s account of the April 18 exploit that generated losses exceeding $300 million across the DeFi ecosystem.
Through a detailed report exhibiting internal communications, on-chain data and independent security research, the protocol maintained that the flaw resided in LayerZero’s own infrastructure and not in a configuration error on Kelp’s part. As a direct response to the incident, the team announced a full migration to the Chainlink CCIP protocol to secure rsETH.
— Kelp (@KelpDAO) May 5, 2026
The Breach LayerZero Could Not Contain
The attackers compromised LayerZero‘s DVN infrastructure, breached two RPC nodes and executed a denial-of-service attack on the remaining nodes. This forced DVN signers to validate a non-existent transaction.
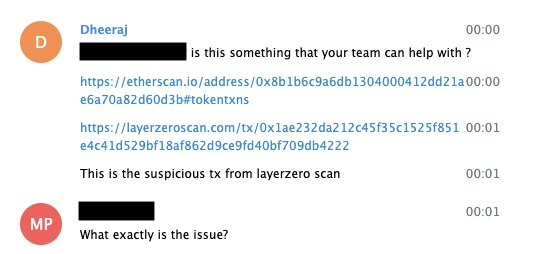
KelpDAO detected two additional fraudulent transactions totaling $100 million and paused its contracts before the damage could spread. LayerZero’s public response came more than 34 hours after the incident and attributed the attack to an RPC-spoofing scheme. However, SEAL 911 researchers concluded that the problem originated within LayerZero’s own trust perimeter.
The group linked the attackers to North Korea with a high degree of confidence and specified that they fraudulently triggered an attestation from LayerZero’s DVN. LayerZero’s own postmortem acknowledged that the attackers accessed its DVN’s RPC list and replaced node binaries. Data from Dune Analytics showed that approximately 47% of LayerZero OApp contracts operated with a 1-1 DVN configuration, and that more than 90% of messages over the past 90 days relied exclusively on the LayerZero Labs DVN.
Kelp’s Configuration Had Been Approved
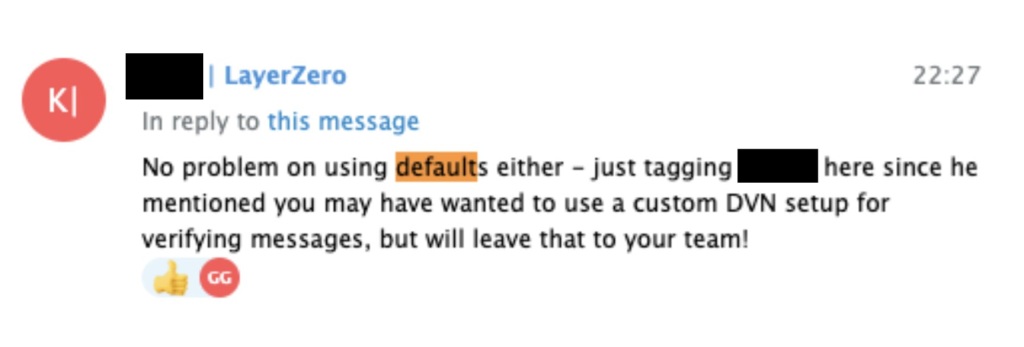
KelpDAO noted that its 1-1 DVN configuration was explicitly approved by a member of the LayerZero Labs team via Telegram, with no risk warning issued across more than two years and eight documented integration discussions. Researchers also found that LayerZero’s AWS deployment exposed a public gateway with no IAM authentication, no WAF and no IP allowlists. The quorum configured at 1 meant that backup RPCs operated as failover rather than as a multi-provider consensus mechanism.
Kelp initiated the migration of rsETH to Chainlink’s Cross-Chain Token standard, whose network handled over $30 trillion in value across seven years of continuous operation through multiple disruptions. KelpDAO also noted that ten addresses shared the ADMIN_ROLE in both the LayerZero Labs and Nethermind DVNs as of April 8, which calls into question the real independence between both operators. A full forensic report will be published once the review is complete.