When Bitcoin was proposed back in 2008, the author of the whitepaper –Satoshi Nakamoto – introduced a novel but simple idea of solving the ‘double spend’ problem.
The idea was simply to duplicate a ledger multiple times and have each copy stored by multiple parties. These parties, also called nodes, would then compete to create the next block by solving complex mathematical puzzles.
The competition was purposely made challenging to ensure that the nodes incur a cost while competing. This last part has attracted criticism especially from the environmentally friendly individuals and institutions who claim that Bitcoin encourages environmental degradation.
Ignoring the negatives, we do find out that this method of governing a blockchain has become quite revolutionary that several consequent blockchain networks opted to adopt it. Over the years we have seen multiple projects come and go and several of them failed because of one problem – security.
Security is one of the most important factors to consider when designing a blockchain and to ensure the network is secure, you need a diverse and decentralized network of nodes. Bitcoin has over the years created this kind of network, however for a majority of the rest, attracting the right number of nodes through the correct balancing of economic incentives has proven challenging.
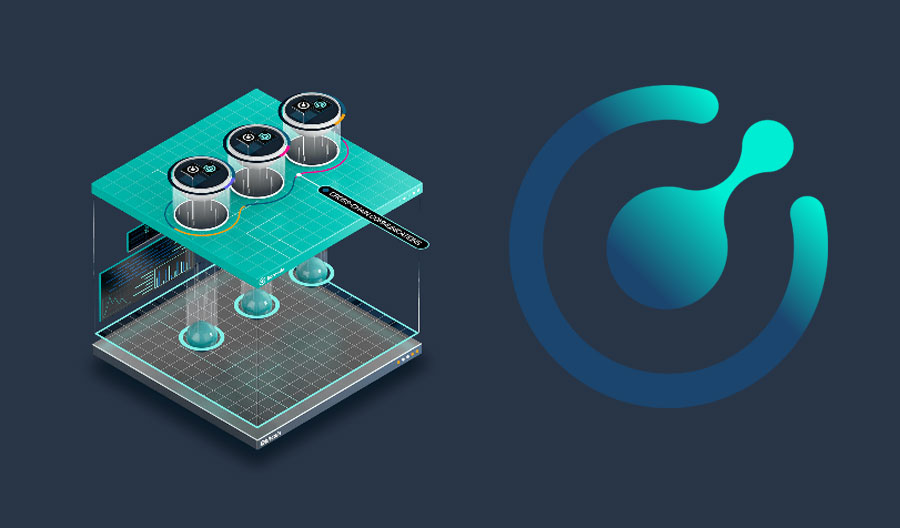
The Komodo Platform was also faced with the same challenge in its initial design phase and to solve the problem (and avoid a potential death trap), the project introduced a novel consensus mechanism called delayed proof of work (dPoW). In the simplest terms, dPoW is a dual prong approach to consensus. It makes use of two systems and suffice to say, one of those is the original proof of work introduced by Bitcoin. Not only that, but Komodo also went ahead to use the Bitcoin blockchain itself to secure its network.
Notarization
It is no secret that Bitcoin is the most secure blockchain right now and this is because it has the largest hash rate of any network. It will be hard for any Proof of Work blockchain to duplicate Bitcoin’s success. Therefore, instead of trying to do that, Komodo chose to take advantage of the Bitcoin security by storing its blockchain data on the Bitcoin blockchain.
Think of this as inherited security and the process of encoding the Komodo blockchain to the Bitcoin blockchain is what is called notarization. There are special nodes present on the Komodo network called Notary Nodes that are tasked with undertaking the notarization.
As opposed to the normal unelected nodes that undertake validation of transactions on the initial blockchain, notary nodes are chosen by stakeholders to represent the rest of the nodes. These nodes are interchangeable and are voted in every year. There are a total of 64 nodes on the Komodo platform.
One thing to note is that the initial blockchain in the delayed PoW system can have any form of consensus mechanism. This includes Proof of Stake (PoS), Delegated PoS, Proof of Work (PoW), Proof of Authority, Proof of History, etc. It does not matter which initial consensus mechanism a blockchain uses. For this system to be effective, it is the latter blockchain that matters.
Bitcoin, despite its class-leading security, could easily compromise its blockchain if it switched to delayed PoW which means trusting another less secure blockchain with its data. However, the opposite is achievable. A less secure blockchain can choose to notaries its data to Bitcoin and take advantage of its hash rate.
Komodo is one such blockchain that has successfully taken this approach making it among the most secure blockchains out there. To learn more about the security Komodo’s delayed Proof of Work (dPoW), check out this blog post by Komodo. You can also dig into Komodo’s multi-blockchain architecture while you at it.