TL;DR:
- Massive Attack: A user identified as Nima received 89 alert emails in less than 30 minutes after moving stablecoins on Ethereum.
- Million-Dollar Losses: So far in 2026, address poisoning scams have drained $62 million, including a single theft of $24 million.
- Technical Impact: The Fusaka upgrade in December 2025 reduced fees, causing USDT “dust” transfers to skyrocket by 612%.
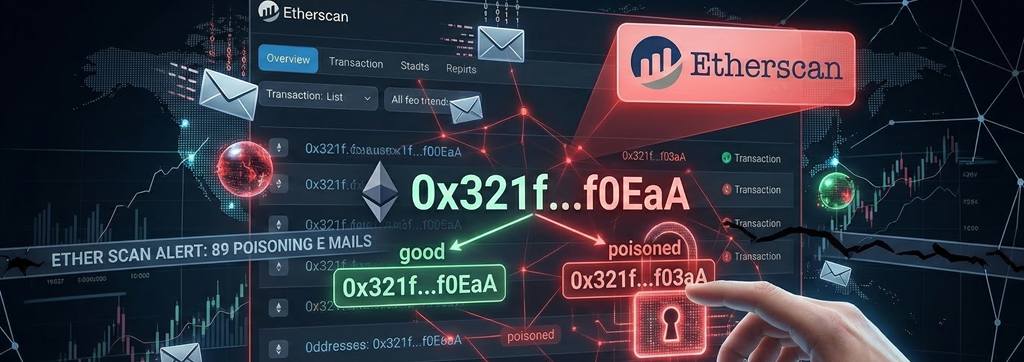
The block explorer Etherscan issued a red alert after detecting a sequence of high-frequency automated attacks. Etherscan’s warning on address poisoning stems from a user case who was bombarded with malicious transactions designed to spoof legitimate addresses in their history.
— etherscan.eth (@etherscan) March 12, 2026
In this regard, the data is alarming: poisoning attempts on Ethereum have a success rate of only 0.01%, but the sheer scale compensates for the inefficiency. Following December 3, 2025, when Fusaka was activated, daily transaction volume increased by 30%, while “dust” transfers (less than $0.01) in USDC jumped from 2.6 million to 14.9 million—a 473% increase.
The malicious technique involves generating addresses that mimic the first and last characters of a victim’s frequent contacts. Consequently, attackers flood the wallet history with near-zero value transfers, hoping the user will copy the wrong address for their next transaction.
Of equal importance is the context of currently low fees. As gas costs decrease, criminals can profitably execute massive attacks, where a single successful large transfer covers thousands of failed attempts.
The Impact of Fusaka and User Security
Furthermore, the speed of these attacks is unprecedented; cases have been reported where thirteen fake addresses were planted just minutes after a real transaction. This underscores the need to use active verification tools to avoid costly human errors.
To mitigate this risk, Etherscan recommends using private labels and its “Address Highlight” feature, which allows for visual differentiation between similar addresses. Additionally, the explorer now automatically labels and hides zero-value transfers to clean up user history.
In summary, address poisoning has evolved from a minor nuisance to a structural threat in 2026. The combination of lower network fees and aggressive automation demands that users verify every character before confirming any fund transfer.










