TL;DR:
- Axios, one of the most widely used JavaScript libraries with 100 million downloads, fell victim to a supply chain attack.
- Malicious versions 1.14.1 and 0.30.4 were active for nearly three hours and injected a hidden dependency containing a remote access trojan.
- No unauthorized cryptocurrency transactions were reported during the attack, although wallet exposure cannot be ruled out.
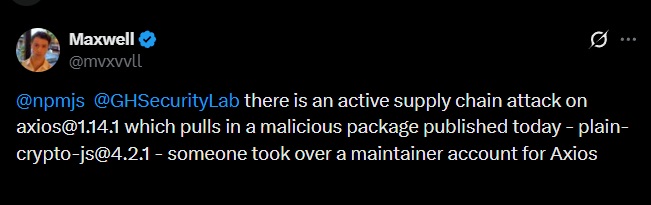
Axios, one of the most widely used HTTP libraries in the JavaScript ecosystem with over 100 million downloads, was the target of a supply chain attack. Two malicious versions of the package —npm 1.14.1 and 0.30.4— were published through the compromised credentials of @jasonsaayman, the project’s lead developer, and remained available for approximately three hours before being removed.
The attack was identified early by the teams at StepSecurity and Socket Security. Feross Aboukhadijeh, CEO and co-founder of Socket Security, explained that the compromised versions did not follow the standard GitHub publishing workflow, which immediately raised suspicions. According to the analysis from both firms, the malicious packages injected an undeclared dependency into the original source code: [email protected], published just minutes before the affected Axios versions.
Axios: Trojan Injection and Remote Access
That dependency executed a post-installation script active on macOS, Windows, and Linux. On macOS systems, the payload delivered a remote access trojan capable of executing commands and deploying additional binaries. The malware also erased its own traces and replaced configuration files with clean versions to evade detection mechanisms, making any subsequent audit difficult by simply inspecting the node_modules folder.
A Rising Modus Operandi
Researchers also identified two additional packages operating through the same mechanism: @shadanai/openclaw and @qqbrowser/openclaw-qbot. This new incident comes just one week after another case of malicious code injection into LiteLLM, suggesting that the frequency of this type of attack is escalating.
No reports of unauthorized cryptocurrency movements or directly affected Web3 projects have emerged so far. However, given that many crypto applications rely on Axios for their API communication, the potential exposure of wallet data remains a concern. Security teams recommend reviewing lock files for the compromised versions and avoiding automatic updates without prior inspection.