TL;DR:
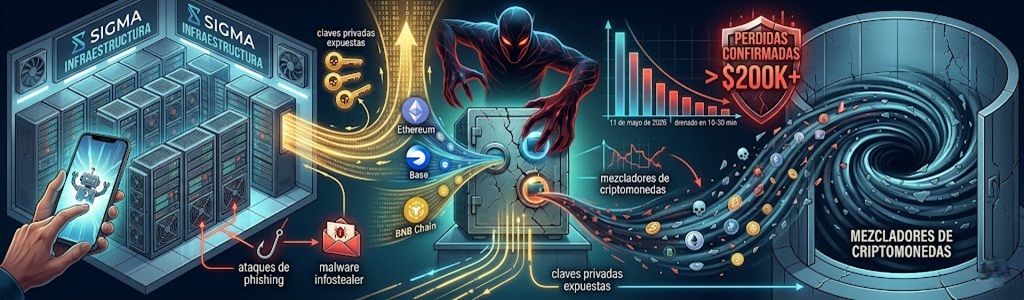
- The attack affected assets on the Ethereum, Base, and BNB Chain (BSC) networks, totaling a loss of over $200,000.
- The compromised wallets were originally generated through the Telegram bot named SIGMA.
- The attacker executed the fund draining in an estimated period of between 10 and 30 minutes on May 11, 2026.
The crypto trader known on X as Unihax0r reported that this Monday, May 11, he lost more than $200,000 after two of his digital wallets were drained. Preliminary reports indicate that the incident is linked to the use of a Telegram bot for asset management.
The trader claimed that he lost control of his funds on Ethereum, Base, and BSC almost simultaneously. Transaction analysis conducted by on-chain specialists indicates that the attacker gained total control over signing operations across multiple blockchains.
Network data shows that this was not a smart contract vulnerability. According to analyst @k0braca1, the absence of malicious token approvals suggests that the incident originated from a leak of the user’s private keys.
The stolen sum includes approximately $125,000 in $POD tokens from the Base network and about $21,000 in $FHE from the BSC network. The attacker even transferred small amounts of ETH to the victim’s wallets to cover the gas cost necessary to complete the withdrawal of the remaining balances.
Vulnerability in Wallets Generated by SIGMA
Community research identified that both compromised wallets had a common origin: they were created using SIGMA, a multi-chain trading Telegram bot. Although the user had imported these addresses into other tools like Rabby Wallet, other accounts not linked to SIGMA remained secure.
This technical distinction reinforces the hypothesis that the bot’s infrastructure may have been the point of compromise. Security researchers suggest that the theft of secret keys could stem from phishing attacks using fake captchas or infections by “infostealer” type malware.
Just got drained or hacked for more than 200k. Sick to my stomach
This is the wallet where the money went:
0xF7cFFC27732a5C9c4E2D592F3E33435F8dDb019AAny help to track the money would be appreciated
— Unihax0r (@0xUnihax0r) May 11, 2026
Unihax0r reported that after reviewing his Telegram account, he found no suspicious active sessions. However, the stolen assets were moved to an external account under the attacker’s control, where on-chain data confirms that the tokens are already being processed through cryptocurrency mixers.
Although assets on the Base network remained at the attacker’s addresses shortly after the event, fraud tracking experts point out that the chances of recovering the funds are slim due to the irreversible nature of transactions.
Trading Bots as a Critical Security Point
This is yet another incident in the trend of security breaches related to automated tools in messaging services. When generating wallets through a Telegram bot, private keys are typically stored within the software provider’s infrastructure.
According to ForkLog research, this delegated custody model could lead to asset losses, as they often lack the robust protections of cold or hardware wallets. The ScamSniffer platform previously reported that malware scams in Telegram groups have increased significantly in recent months.
A relevant precedent occurred in September 2025, when the Banana Gun bot suffered the exploitation of 36 wallets, resulting in a loss of approximately $1.9 million in ETH. These events expose the operational risks of integrating private key management into third-party applications without institutional-grade security protocols.