TL;DR:
- Zerion confirmed that an employee lost approximately $100,000 from internal wallets following a social engineering attack linked to North Korea.
- The attacker accessed active sessions, credentials, and private keys from hot wallets used for internal testing, so no user funds were compromised.
- The Security Alliance identified 164 malicious websites connected to group UNC1069, active since February 2026 and targeting crypto and Web3 firms.
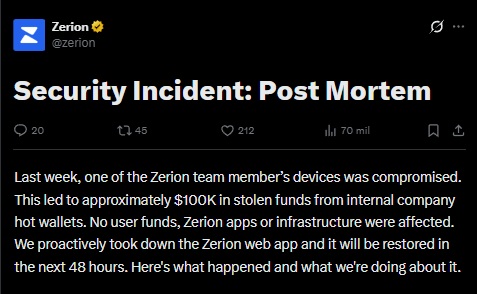
A Zerion employee fell victim to an AI-powered social engineering attack linked to a North Korean (DPRK) threat actor, as confirmed by the company itself in a statement published on X. The incident resulted in the theft of approximately $100,000 from internal hot wallets used for testing and internal operations. No user-related funds were compromised.
The attacker managed to access active sessions, credentials, and private keys from the team’s internal wallets. Zerion clarified that its wallet is fully self-custodial and that no team member has access to users’ private keys or seed phrases. The company’s mobile apps, browser extension, backend infrastructure, and social media accounts also remained intact.
Zerion Responds Quickly and Seeks to Reassure its Community
The post-mortem of the incident notes that the attack was sophisticated and planned, not driven by mere opportunity. Upon detecting the breach, the Zerion team took immediate action: it locked the deployment infrastructure to prevent the attacker from publishing malicious versions on the company’s domains, placed the web application in maintenance mode, and rotated all exposed credentials and private keys. Multisig accounts were also reconfigured. In addition, each team member ran an analysis script on their devices to detect malware similar to that used in the attack.
The company worked with the teams at Blockaid, ZeroShadow, and ChainPatrol to identify and request the removal of the attacker’s wallets and accounts. The stolen funds were traced to specific addresses, which were reported to the relevant authorities.
The Security Alliance (SEAL) has been investigating similar attacks from February 6 through April 7, 2026, and has already identified 164 malicious websites linked to UNC1069, a group backed by North Korea that targets crypto and Web3 companies. SEAL warned that the group uses fake Zoom and Microsoft Teams calls, as well as software attacks to steal funds and sensitive data.
North Korea: The Biggest Enemy of Crypto Security
This incident is part of an already established trend in the industry. According to the most recent report from the FBI’s Internet Crime Complaint Center, cybercrime losses exceeded $20.8 billion in 2025. That same year, more than 22,000 complaints involving artificial intelligence components were recorded, underscoring the growing scale and sophistication of attack vectors targeting the crypto ecosystem.