Everything around us is gradually being digitized. This process is advancing rapidly, and security and privacy in data processing have become fundamental priorities when evaluating a project. For this reason, Nillion aims to revolutionize the mechanisms for handling sensitive data by avoiding reliance on traditional blockchain infrastructures. Throughout this article, we will explore its value proposition, underlying mechanisms, and the potential relevance it may hold within the industry and for its future.
What is Nillion?
Nillion defines itself as a decentralized network focused on ensuring the secure and efficient processing of data through advanced cryptographic techniques. Unlike conventional blockchains, which record each transaction in chained blocks, Nillion operates using methodologies such as Multi-Party Computation (MPC), Fully Homomorphic Encryption (FHE), and Zero-Knowledge Proofs (ZKP).
These technologies allow data to be processed collaboratively without revealing confidential information, offering a robust solution for applications requiring high levels of privacy. The innovative foundation behind Nillion is based on the concept of Nil Message Compute (NMC), developed by Miguel de Vega, which enables the handling of sensitive data without sacrificing efficiency.
How Does Nillion Work?
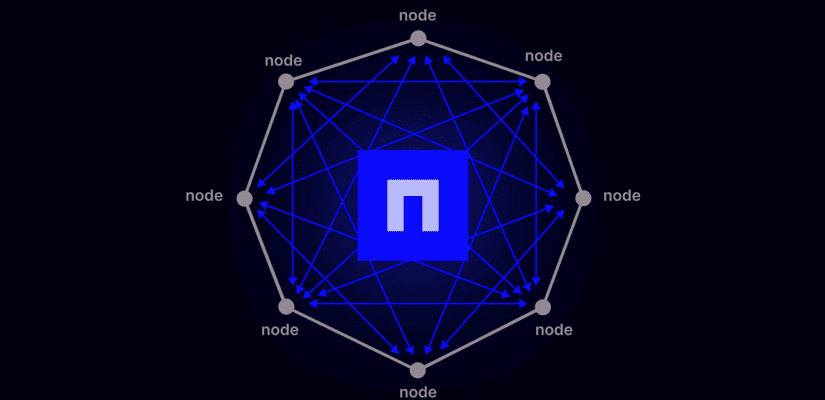
Nillion’s architecture is organized into several layers that work together to provide secure and decentralized data processing.
Processing Layer
First, the processing layer is responsible for executing computations on the data using cryptographic algorithms that keep the information encrypted throughout the entire process. This layer ensures that sensitive data is never exposed in plain text.
Coordination Layer
The next layer, known as the Coordination Layer, manages the interaction between nodes and the distribution of tasks, ensuring optimal data flow and properly synchronized operations. This layer leverages consensus technologies and blockchain-based control systems to maintain a shared global state, facilitating the administration of payments, resources, and governance.
Connectivity Layer
Lastly, the connectivity layer handles the communication infrastructure, linking all nodes and ensuring the network’s robustness and responsiveness.

Nillion’s Special Tools
In addition to these layers, Nillion incorporates special components to enhance its security and functionality. Among them is the cryptographic preprocessor, which encrypts and decrypts data before processing begins, and the Secure Resource Vault, which redundantly stores sensitive information and cryptographic keys.
The Coordination Interface facilitates communication between these components, while the Public Particle Database allows for the exchange of non-sensitive data. Complementarily, the Program Library and the Authentication and Access Control Service provide tools and protocols for developers to build secure applications with the highest level of privacy.

What is the NIL Token and What is it Used For?
The $NIL token is the utility asset that underpins the Nillion network. With a total supply of one billion units, it plays multiple roles within the ecosystem. NIL holders can use it to secure the coordination layer through staking, which in turn grants them voting power in governance decisions and validator selection. In this way, the token becomes a crucial tool for managing the network and collective decision-making.
Additionally, NIL is used as a means of payment for resource management. Users pay with NIL to submit secure processing requests and to access the blind computing functions offered by Nillion. This token economy helps maintain a steady flow of revenue that supports the network’s development and operation. On the other hand, infrastructure providers who join the Petnet clusters receive rewards in NIL, which incentivizes network expansion and ensures operational stability.
Is NIL a Good Investment?
The evaluation of NIL as an investment depends on several factors related to the adoption and growth of the Nillion ecosystem. As a core element of the network, its value is primarily influenced by the demand for its services and the expansion of its infrastructure, particularly in areas such as secure and private computing, which are increasingly sought after by companies and projects looking for alternatives to traditional solutions.
Nillion’s ability to offer better privacy solutions could make it a suitable tool in fields like artificial intelligence and identity management. If the network manages to attract a solid user base over time and earns loyalty from both developers and enterprises, the demand for NIL as a means to access these services could increase—potentially driving the token’s value upward.
However, it is important to consider several significant risks. The adoption of emerging technologies like Nillion is still in its early stages, raising questions about whether it will be able to achieve mass adoption. Additionally, the crypto market is volatile and subject to external factors such as government regulations, competition from other platforms, and the evolution of market perception regarding the technology.
As with any investment, all risks should be carefully assessed, and the project’s goals and future prospects thoroughly analyzed. While the NIL token has the potential to be an interesting asset within an innovative ecosystem, it is crucial to conduct exhaustive research and manage risks appropriately.
Conclusion
Nillion is an innovative solution for secure data processing. It has the potential to overcome many of the limitations of traditional blockchain technologies. Its advanced architecture, combined with the use of cutting-edge cryptographic techniques, enables secure, efficient, and scalable data processing while maintaining a high standard of privacy.
Nillion offers a promising shift for the development of applications requiring a high level of information protection in critical sectors such as artificial intelligence, decentralized commerce, identity management, and more. The commitment to a decentralized and secure model could mark a turning point in how data is handled in this new era











