Most of the smart contracts issued on the Ethereum network utilize reused code. This is the revelation shared by a group of researchers from the University of Maryland in collaboration with another team from Northeastern University.
Their conclusion is based on a research they undertook that analyzed Ethereum’s blockchain from inception to its five millionth block. The study, which is entitled “Analyzing Ethereum’s Contract Topology,” looks at the composition of smart contracts, their usage, and relation to each other. The researchers also queried the Ethereum Virtual Machine dubbed Geth to analyze the level of user adoption and interaction with the smart contracts.
What the researchers found was that a majority of the smart contracts are exact or near-copies of other contracts and according to the researchers this represents a major problem to the Ethereum ecosystem if the copied contract has a vulnerability or bug. Current stats show that as much as 1.2 million contracts have been created on the Ethereum network, however, the researchers were able to group these contracts into 5877 contract clusters according to the uniqueness of the byte-code underlying the contracts.
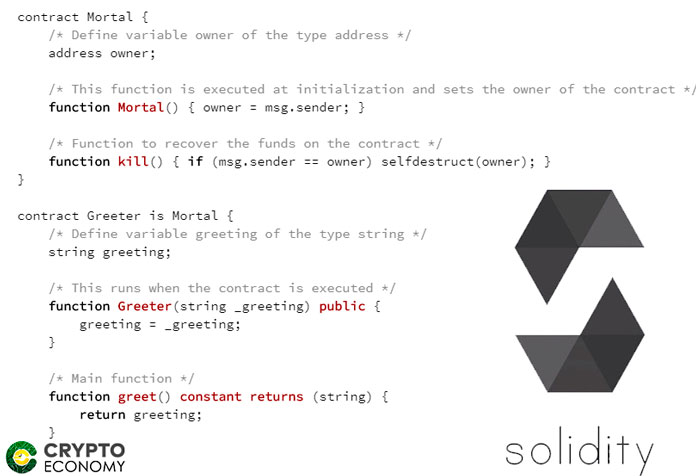
Code reuse is very popular in the software development world, however, the open-source nature of the blockchain has led to extremely high levels of code reuse that threatens the security and efficiency of smart contracts especially on the Ethereum ecosystem. In fact, the study found out that most smart contract code on the Ethereum platform is created by other contracts instead of users.
Another interesting revelation that the study divulged was that a majority of the smart contracts on the platform have “never been interacted with.” This means that the intended users have not interacted with this code. This reveals that most of the code on the Ethereum platform is dormant.
The security concerns that this report puts forth are not unwarranted. In the recent past, a smart contract bug found on the Icon network disallowed contract creators from suspending transactions on the network but allowed everyone else to do the same. The bug was, however, fixed right after the bug discovery. Security vulnerabilities and bug discoveries are not exceptions in the industry and code reuse just magnifies the effect of this problem.